Ubuntu 18.04 and unprivileged LXC
I use this LXC containers for two reasons:
-
To have lightweight local environment for trying AWS EC2 server environment installation scripts. Those scripts changes config files in /etc so I don’t want to run them on my host system. Running them on AWS is slow (copying script there) and expensive.
-
For my attempts to prepare LXC container that embeds complete developement environment (Eclipse, PostgreSQL, VS Code, GIT, Gradle, …). All those tools will be properly set. So upgrade of Eclipse will be done once in template and all developers can just make copy and benefit from it. Also developing multiple versions of app, each using different database schema, will be much easier.
Notes:
-
Docker is not really usable for this tasks because it should contain only single app
-
I prefer unprivileged containers because I like Principle of least privilege rule. In this case LXC container does not have access to host hardware.
Installation is simple but there is one pitfall.
Install LXC:
sudo apt install lxcCreate file ~/.config/lxc/default.conf with content:
lxc.include = /etc/lxc/default.conf
lxc.idmap = u 0 100000 65536
lxc.idmap = g 0 100000 65536Add into file /etc/lxc/lxc-usernet (replace REPLACEME by your login):
REPLACEME veth lxcbr0 10Create container, choose any distro you like:
lxc-create -t download -n my-container-nameStart container:
lxc-start my-container-nameUnfortunatelly it says it cannot be started:
The container failed to start. To get more details, run the container in foreground mode. Additional information can be obtained by setting the –logfile and –logpriority options.
Huh, we found pitfall 😉 Trying to start with logging on:
lxc-start my-container-name --logfile lxc.log --logpriority debugExposes better error message in log file:
Permission denied - Could not access /home/jarek. Please grant it x access, or add an ACL for the container root
So we need to add (as host computer root) ACL for AppArmor. It adds execution right (to allow traversal) for user 100000 (proces with PID 0 in container):
setfacl -m u:100000:x /home/jarek/
setfacl -m u:100000:x /home/jarek/.local
setfacl -m u:100000:x /home/jarek/.local/share
# It may be inspected by
# getfacl /home/jarek/
# It may be later removed by
# setfacl -x u:100000 /home/jarek/Then we can start container:
lxc-start my-container-nameAnd finally connect it:
lxc-attach my-container-nameResult should be like:
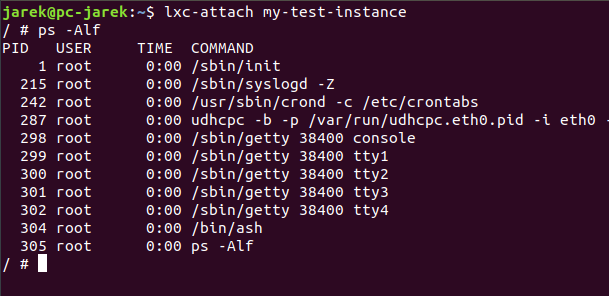
Great, now it works! And it is really isolated from your host machine.
Tags:
